Articles
Share
If you’re a building manager, an events organiser, or a facilities or operations manager, your operations must comply with safety regulations. It’s imperative to mitigate security threats and operational risks, ensuring the safety and well-being of your occupants and maintaining the efficient operations of your organisation.
Integrated security solutions help prevent a range of threats to your facility, whether they’re security threats or indoor hazards. Furthermore, they also allow you to remain compliant with safety regulations, so that you don’t face regulatory fines or legal liability.
As an integrated security solution, we’ve worked with a range of clients, from event organisers to residential building owners and managers. We’ll outline in this guide the same advice we give these clients: starting with the regulations you should be compliant with.
To understand how integrated security solutions reduce liability and operational friction, it is important to examine the frameworks governing commercial properties in Singapore. These include, but are not limited to, the following:
The Personal Data Protection Act (PDPA) is Singapore’s principal legislation governing the collection, use, disclosure, and care of personal data by organisations.
The law was designed to protect individuals’ personal information from exploitation or leakage, while recognising the legitimate need for businesses to collect and use data for reasonable purposes.
Under the PDPA, organisations must adhere to several key obligations, including:
The Police Licensing and Regulatory Department (PLRD) is a specialised division of the Singapore Police Force. Rather than being a standalone law itself, it is the statutory body responsible for administering and enforcing the Private Security Industry Act (PSIA).
The PLRD’s primary mandate is to maintain standards across the private security sector. To achieve this, it regulates several key areas:
The Workplace Safety and Health Act (WSHA) is the primary legislation concerning the safety, health, and welfare of persons at work in all workplaces in Singapore. It was enacted to replace older, more reactive laws and create a strong safety culture based on risk management.
The WSHA operates on the principle that those who create risks are the ones best placed to manage them. As such, it places liability on employers, self-employed persons, principals, and occupiers of the premises:
Integrated security solutions help you meet these compliance requirements in the following ways:
The collection of personal data is unavoidable at commercial property entrances.
However, the traditional “clipboard and pen” registration method at the front desk is a major liability. Leaving physical logbooks open allows visitors to see the names, phone numbers, and arrival times of those who signed in before them, which directly violates the PDPA.
Digital visitor management systems solve this problem by capturing and encrypting guest credentials at self-service kiosks or via pre-registered QR codes. This data is stored securely in the cloud, removing the risk of public exposure.
Furthermore, advanced platforms handle biometric data—such as facial recognition templates used for high-security areas—by converting them into encrypted mathematical hashes rather than storing raw images, ensuring complete data privacy.
The department encourages commercial facilities to move toward Outcome-Based Contracting. This means shifting the focus from simply paying for a required number of physical guards to proving that the security measures actually yield results.
Deploying an integrated ecosystem featuring a centralised command centre and AI video analytics allows you to align perfectly with these regulatory standards.
Rather than relying on books, which are vulnerable to tampering or falsification, digital tracking and automated incident logs provide tamper-proof, transparent records.
This level of digital auditing satisfies reporting requirements and demonstrates that your facility operates under active, verifiable surveillance.
Under the WSHA, building owners and employers are legally obligated to take reasonably practicable measures to ensure the safety and health of every person on the premises.
Manually policing vast industrial parks or busy commercial lobbies for safety infractions is virtually impossible for a human team alone.
This is where AI video analytics and intelligent facility solutions become critical.
Networked systems can be calibrated to detect safety anomalies, such as an individual entering a hazardous logistics zone without a safety helmet or a sudden, dangerous crowd build-up in a lobby. Coupled with environmental sensors that monitor for early indicators of fire, water leaks, and toxic gas, an integrated infrastructure provides continuous hazard monitoring that satisfies legal safety obligations.
Managing risk in a commercial or industrial facility is an active, continuous challenge. As such, integrated security solutions provide the following benefits to building owners and organisations:

Tasking a security officer with monitoring multiple static screens or conducting repetitive patrol routes for extended periods significantly increases the likelihood of human error.
Human attention naturally wanes over time, creating vulnerabilities in security protocols.
Integrated solutions resolve this by shifting the burden of routine monitoring to artificial intelligence and automated sensors.
This ensures that human operators at the centralised command centre and on-site officers remain highly alert, ready for emergency response.
Traditional security setups suffer from massive blind spots since a physical guard cannot be in more than one place at once.
An integrated security system replaces limited physical presence with digital omnipresence.
By deploying a network of smart cameras equipped with video analytics, you can establish digital lines around the entire perimeter of your property. If an intruder crosses these lines or loiters after hours, the system detects it instantly.
This proactive coverage extends beyond criminal activity; integrated environmental sensors also monitor the facility for water leaks, smoke, and power failures, ensuring that operational risks do not go unnoticed.
Relying entirely on a large, stationary team of guards to secure a large-scale or multi-zone property is prohibitively expensive and inefficient.
Adopting technology, such as automating gate management, visitor registration, and perimeter monitoring, drastically lowers the requirement for a physical headcount. This allows commercial properties to reduce their security operating costs by substantial margins while increasing their total surveillance coverage.
The features you can expect from integrated security solutions are as follows:
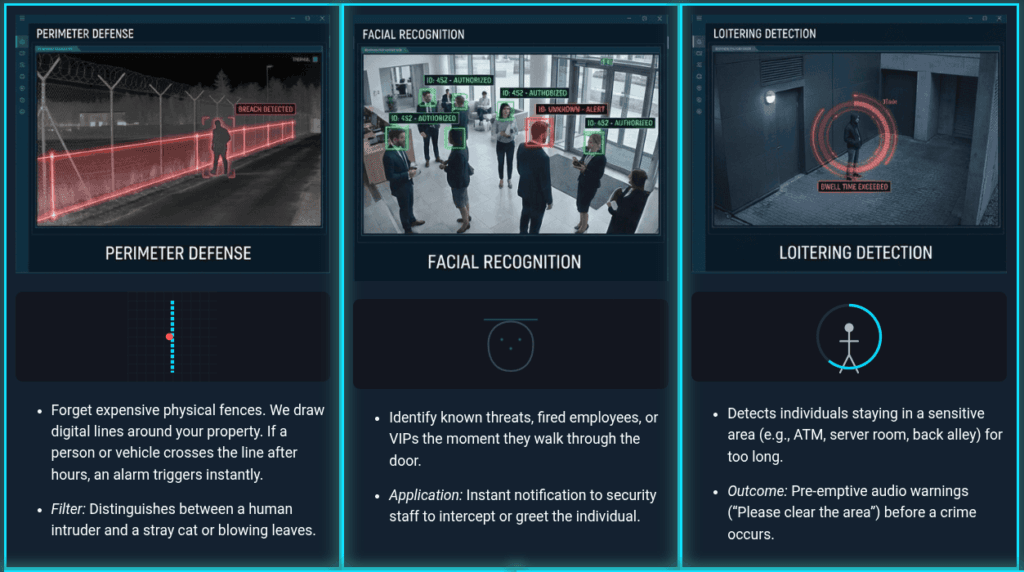
Integrated systems utilise a neural network of AI-powered cameras that transform video feeds into intelligent sensors. These systems scan for specific behaviours and patterns 24/7, filtering out environmental noise such as swaying trees to ensure that security teams receive only alerts that require genuine intervention.
These AI-powered systems are capable of the following functions:
A security system is only effective if it remains operational during an emergency.
Integrated solutions are engineered with high levels of redundancy, featuring uninterruptible power supplies (UPS) and failover internet connections.
This ensures that even in the event of a local power cut or a network outage, the facility remains under constant surveillance and the link to the command centre stays active.
Protecting the integrity of security footage and visitor logs is a critical part of risk management.
All data transmissions within an integrated ecosystem are encrypted and stored in secure cloud environments. This prevents unauthorised digital tampering and ensures that all records remain admissible and intact for legal or insurance audits.
Integrated visitor management does more than just register guests; it acts as a screening gate.
By connecting the digital entry kiosk to a central watchlist or blacklist, the system can alert on-site security and the command centre if a known troublemaker attempts to enter, or a former employee tries to access unauthorised areas.
This allows for a discreet intervention before the individual gains access to the building.
At Focus Group Security, we specialise in protecting properties with resilient, intelligent security systems.
Our specialised Command Centre, paired with our iFS360 system, provides you with a robust integrated security solution. This technology-enabled approach makes our system more efficient and alert than standard stationary security services.
Our solutions do not merely satisfy the compliance obligations under PDPA, PLRD, and WSHA requirements—they actively enhance your operational efficiency
Ready to de-risk your facility? Contact us today to speak with our consultants about a customised integrated security roadmap.
Our systems receive regular over-the-air firmware and software updates to ensure the neural networks are trained against the latest security challenges.
No specialist IT staff are required on your end. The system is managed and monitored 24/7 by our team at the Command Centre, providing a fully managed service.
Yes, we can sync the system with your HR software to automatically update or revoke access permissions whenever an employee joins or leaves the organisation.
The moment our Command Centre operators verify a genuine threat via the live feed, the nearest ERT vehicle is dispatched instantly, with the operator providing live tactical updates to the officers en route.
Focus Security Services